By Greg Mercer
Ever since al Qaeda in Iraq rebranded itself as the Islamic State in Iraq and the Levant in 2013 and split from al Qaeda at large, there has been some confusion as to how exactly to refer to the entity. The extremist group’s growing paramilitary force is attempting to create an independent state governed by a Wahhabist ideology. It has been referred to as the Islamic State, IS, ISIS, and ISIL, with no convention appearing to have emerged, and there has been just as much coverage about the debate surrounding this nomenclature vacuum.
The Associated Press, writing in June of 2014, notes that the Arabic name Al-Dawla Al-Islamiya fi al-Iraq wa al-Sham translates to the Islamic State of Iraq and al-Sham, and that al-Sham, which encompasses the Middle East from southern Turkey to Egypt, and is also referred to as “the Levant.” Based on this interpretation, the AP argues that “ISIL” is both the most accurate translation and a clear indication of the group’s aims, as “Islamic State in Iraq and Syria” implies that the group is interested in only two countries. Finally, they note that ISIL is the abbreviation used by the United Nations.
Ishaan Tharoor, writing for the Washington Post in June of 2014, notes that ISIL is used by the State Department and President Obama. However, he points out that the translation leading to ISIL might not be infallible. Citing Hassan Hassan, he notes that “the Levant” might be considered an outdated term, and that “Greater Syria” can be used to refer to the area in question, in which case the Islamic State of Iraq and Greater Syria, and thus ISIS, could be appropriate. He also notes that ISIS is attractive for the way it rolls off the tongue. Tharoor says that the difference between ISIS and ISIL is not as politically charged as, for example, the difference between “Burma” and “Myanmar.”
In September of 2014, Ian Black, writing for The Guardian (which uses ISIS as its in-house standard), noted the sordid history of Islamic State names, and explained that the French government had offered up the term “Daesh,” the Arabic acronym for Al Dawla al-Islamyia fil Iraq wa’al Sham, and which is disliked by Islamic State supporters for notably leaving out the “Islamic” signifier. CNN covered this policy as well.
”You have to name things correctly,” French Foreign Minister Laurent Fabius told Christiane Amanpour. “They are not a state… they are not representative of Muslims.”
Fabius noted that using the term, which is disliked by extremists for its pronunciation similar to Arabic words for “trample,” or “crush,” is an appropriate response to the group’s brutality. Daesh, then, is a much more politically charged name than IS, ISIS, or ISIL, chosen not just for accuracy, but also for the connotation that it carries for the enemy. It also, notably, leaves out “Islamic,” an attractive option for those who desire to make it clear that these extremists are not representative of Islam or Muslims.
Among this debate though, there is an underlying solidarity. The news of France’s refusal to use Islam-based names came alongside their addition to the forces conducting strikes against targets in Iraq. President Obama might have used a different term than France, but he did so in praising France’s military actions.
Referring to the term Daesh, Army Lt. Gen. James Terry said, “Our partners, at least the ones that I work with, ask us to use that, because they feel that if you use ISIL, that you legitimize a self-declared caliphate. … They feel pretty strongly that we should not be doing that.”
A Google Trends search for ISIS, ISIL, Islamic State, and Daesh reveals the overwhelming popularity for ISIS among Google searches:
 Google
Google
While some of the searches for ISIS can be attributed to it being a word with other connotations (an Egyptian goddess, for instance), the search volumes for all of the terms appear to spike at the same times, indicating major news events, with a much higher volume of searches containing ISIS than the other names. While this might not indicate which is the most popular among governments or news outlets, it shows that ISIS seems to be the name of choice for Google users, and the general public.
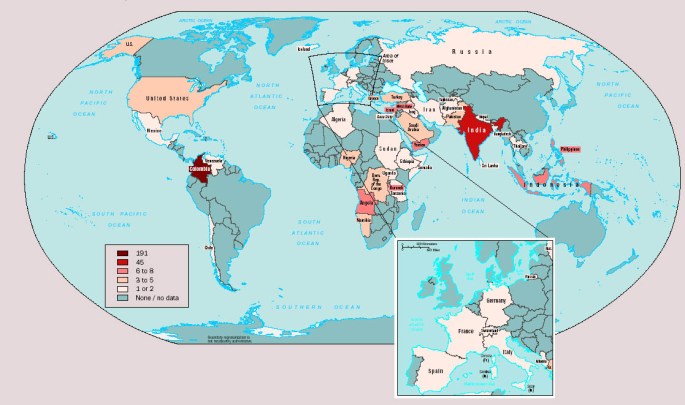
Regardless of the naming conventions that they adopt, many countries see a common threat in Iraq and Syria.
(Image Credit: Wikimedia Commons)